Menu bar. Lock icon. Nothing else.
When a credential arrives the lock opens and shows a live entry with a TTL countdown. Copy any field to the clipboard with a click. When the timer expires, the entry vanishes — nothing remains.
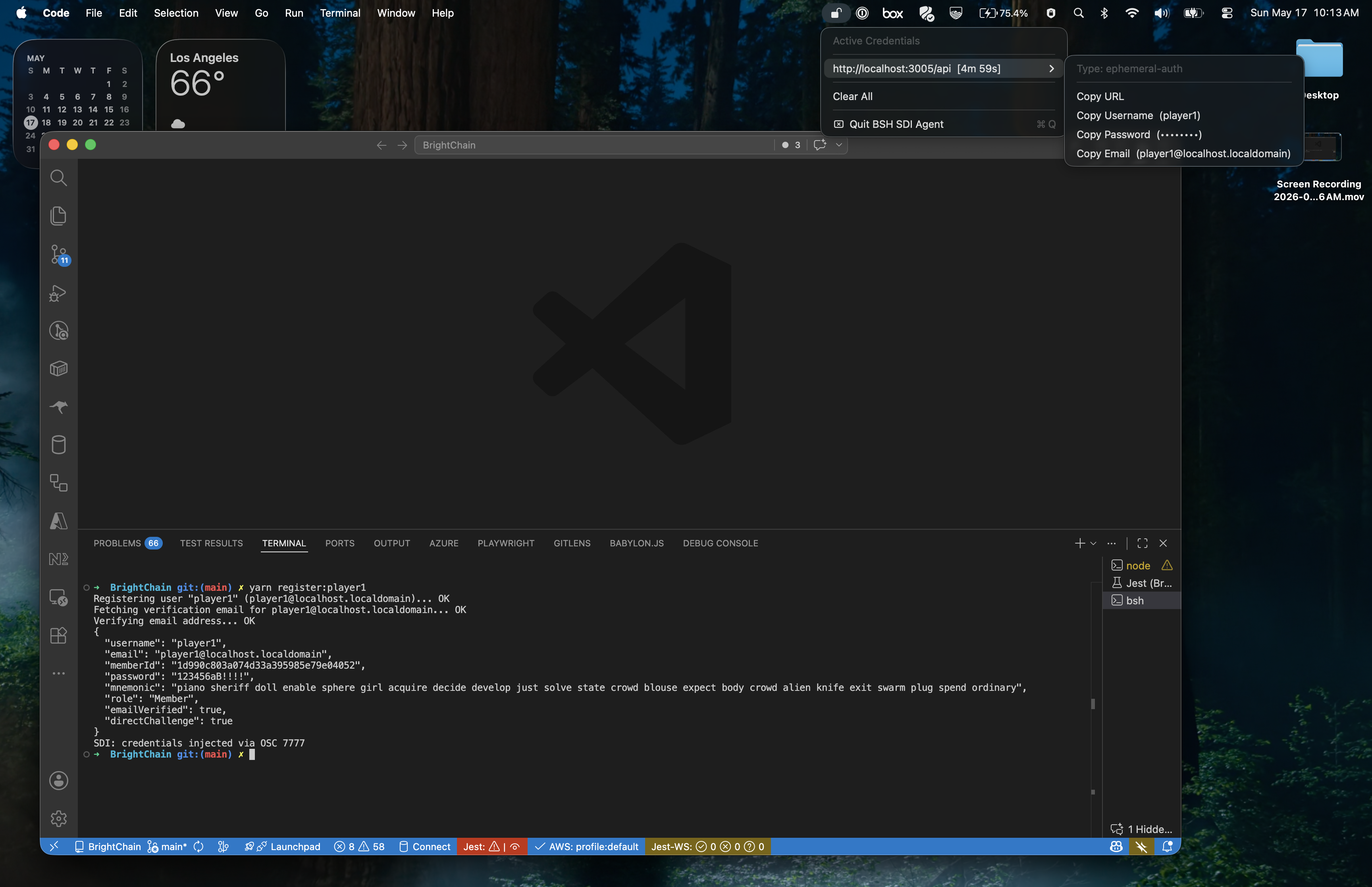
Full demo: BSH shell → bsh-inject → OSC 7777 → SDI
Agent decrypts and shows credential in menu bar.